

sāf.ai
Data, Evolved.
Resiliate
Data resiliency & integrity platform
Immunize your data from ransomware, data theft, and other cyber threats.
TM

Resiliate is Data-as-an-AI
First Protect. Then Alert.
Data interwoven with its own neural net enables data-centric security that cannot be bypassed (unlike perimeters) - protecting itself against:
- unauthorized access and changes
- data corruption and destruction
- data exfiltration
Data becomes immune to costly cyberattacks, such as ransomware and data theft, as well as human error.

Nullify the Impact of Breaches
Reducing RPO to Seconds and RTO to Minutes
Minimize Data Loss
Built-in, high-fidelity Recovery Point capability provides near-zero Recovery Point Objectives (RPO) (0.1 seconds to 1 second) for local volumes and anywhere between 5 and 300 seconds for remote volumes.
Maintain Business Operations
Resiliate’s AI tracks all “clean memories” of each data block in real-time – eliminating much of the manual and error-prone processes of recovery. Recovery Time Objectives (RTO) are reduced to systems I/O and compute bounds.
Simplify & Lower Cost of Recovery
RTOs reduced to minutes (rather than days or weeks) because of near-zero data-cleanup requirements. Downtime, cost of recovery, and TCO are all significantly less with Resiliate than with alternative solutions.
What Matters Most After a Breach
Time to Resume
(get back to business quickly)
Truly Resilient – Resume Operations in Minutes Rather than Days or Weeks
- In the event of a Ransomware attack, files revert themselves – either automatically or on-demand.
- Even if all AI/ML automation fails, data remains resilient (and immediately available) via atomic copy-on-writes, and (optionally) replication over decentralized blockchain storage.
Data Leakage Prevention
(stop data theft)
Limiting the Threat of
Theft & Doxxing
- Data Leakage Protection (DLP) functionality is now integrated directly into each file and data block.
- Files and data can actively raise alarms and events to existing security subsystems.
- Data and files act as their own SIEM event generators and controls.
Immutable Forensics
(understand the damage)
Transparency Into What’s Happening With The Data
- Maintain an immutable record of the complete history of your data and all its metadata.
- Each file can expose all prior “versions” to you simultaneously.
- Data and files now have built-in authorization and audit controls.

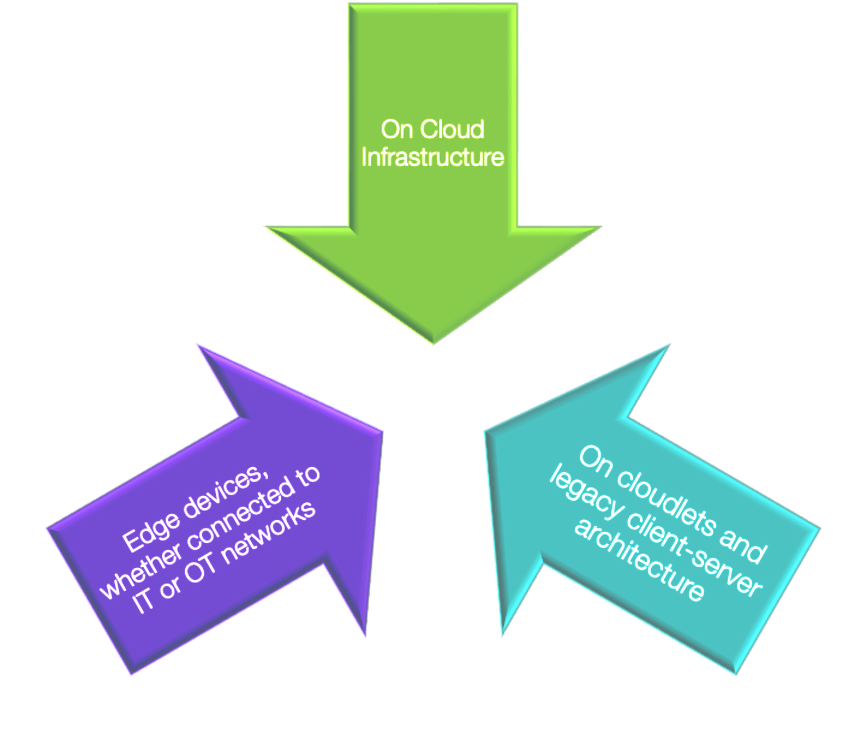
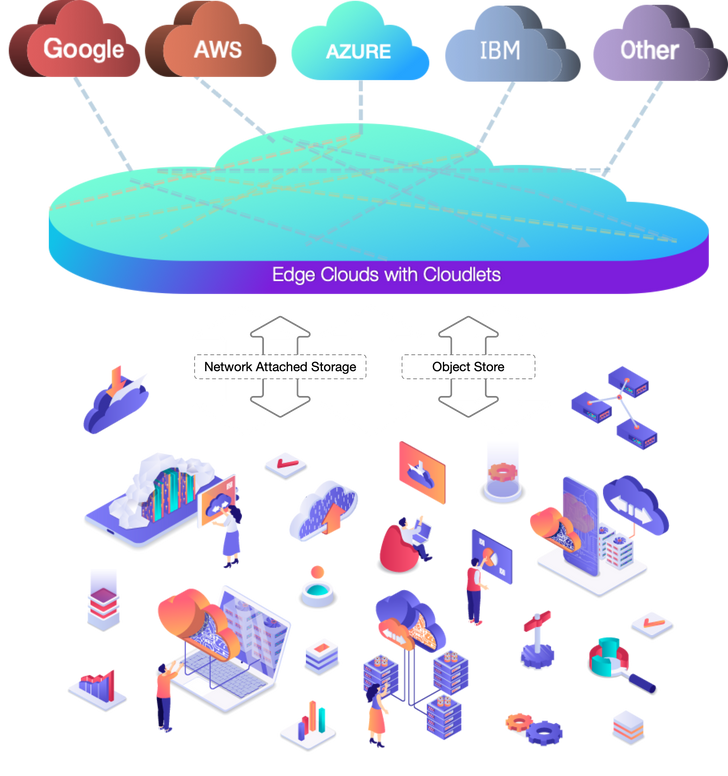
Resiliate Works Everywhere
- Resiliate is deployed as a network-attached storage (NAS) or as a key-value store: users simply serve data from a Resiliate store to enable its self-securing abilities.
- As a POSIX filesystem, Resiliate presents itself like any other network drive and can be used with any type of file.
Plays Well with Others
- Works with everything: edge devices, in the cloud, IoT systems.
- Bridges the gap between legacy and modern computing by providing a path for legacy systems on to transparently interconnect with any cloud-backed storage (supports S3 and Azure blob API).
- Directly supports the efforts of operational automation and cloud adoption across industries through simplified security.
- Lowers technology debt by bridging the gap between legacy and modern systems.
- Works off-line and on air-gapped environments.


Bridging Cybersecurity and Cyber Resilience
Resiliate provides software-defined, zero-trust Security Enclaves for critical systems and complex security policy requirements.
Simplifies security operations by providing data-centric CRUD authorization, context-sensitive integrity and confidentiality, as well as resilient data availability all in one, unified solution.
Provides and enables controls from standards such as NIST 800-53R5 (e.g., Resiliate enables customers to comply with CMMC 1.0 at up to IL5).
Reduce time to resume operations and restore any data loss.
Near-instantaneous rectification of disastrous impact.
Provides and enables deeper controls over data leakage and reduces data exfiltration across multiple environments.

Auditing and Compliance

Resiliate Provides Unique Audit Capabilities
and Insights Into Your Data
Provides deep forensics and audit trails for everything that touches the data.
Provides and enables controls from standards such as NIST 800-53R5 (e.g., Resiliate enables customers to comply with CMMC 1.0 at up to IL5).
Data and files now have built-in authorization and
audit controls.
• Data and files become “compliant by default”
with a multitude of compliance regimes, including NIST 800-*, ISO 20k1-*, PCI, and HIPAA.
• Data readily and more easily integrates with existing compliance tools.

Resources

Learn how Resiliate's unique approach to data security and data resiliency inherently protects against data exfiltration with 'Protect First. Then Alert.'
Learn how backups were never designed to be a security tool and other ways they fall short as a data security solution.
Learn about the core technology behind Resiliate and Resiliate architecture here.
For MSPs, MSSPs, and other potential partners. See how our Partnership Program can add to your business offerings and help your end customers fill the gaps in their data security programs.
Your data is important to us. Learn what data we collect, how we store it, and what we do with it here.
About us
sāf.ai's mission is to make effective data security accessible to everyone.
Data is the fuel that powers any organization.
The need to effectively secure that data becomes more urgent as we struggle to keep up with the pace of data creation and the evolution of technologies that use that data.
We believe that data privacy and security is a fundamental right that should be attainable for all organizations – regardless of size and financial means.
Connect with us
1-888-99-SAFAI (997-2324)
info@saf.ai
support@saf.ai

No matter what gets
into your network,
the core data always
maintains its own Confidentiality, Integrity, and Availability